- DataMigration.AI
- Posts
- Your Cloud Has Been Leaking for Months. Here's Proof.
Your Cloud Has Been Leaking for Months. Here's Proof.
Clear cloud architecture.
What No One Checks.
Cloud migration can hide a million-dollar risk.
Security gaps start before your migration even ends.
Identity is now your real cloud perimeter.
Build security in day one, or pay for it later.
The uncomfortable truth leaders are ignoring in 2026
You are not struggling with cloud adoption anymore.
You are struggling with control.
By 2026, nearly 68% of businesses are increasing cloud spend, but most of them are not be increasing visibility, governance, or security maturity at the same pace.
The cloud was supposed to make your business faster, leaner, and more competitive. For many organizations, it has. But it has also introduced an entirely new category of risk that most migration projects leave completely unaddressed.
And that oversight is costing companies millions before anyone realizes what is happening.
Your cloud migration should not be a gamble with your organization's future. If your organization is planning or re-evaluating its cloud environment, start here:

Understand where your architecture is misaligned before it becomes a liability.
The shift you must understand before it costs you
Cloud security is no longer a technical layer.
It is a business function.
In 2026, leaders are being forced to rethink cloud not as infrastructure, but as an operational backbone tied directly to revenue, continuity, and compliance.
The companies that win are not the ones with more tools.
They are the ones with:
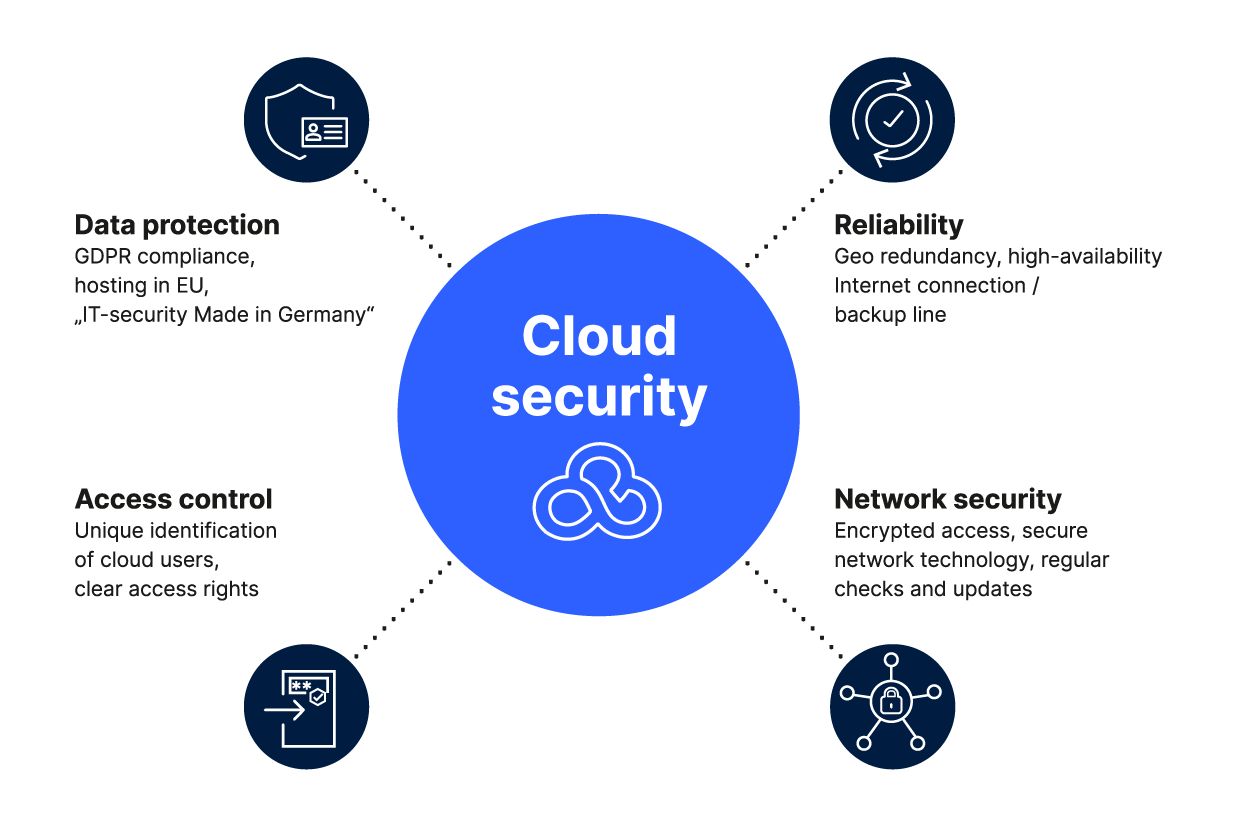
Clear cloud architecture
Intentional workload placement
Continuous security visibility
You Are Protecting the Wrong Thing.
Most organizations still think about cloud security the way they think about a physical office building. Build a strong perimeter. Control who comes through the front door. Assume that anything inside is safe.
That mental model is not just outdated. It is actively dangerous.
Your remote team is not working from a single controlled location. Every home router, every coffee shop connection, every personal device that ever touched your cloud environment is a potential entry point. The traditional perimeter dissolved the moment your team went remote. Most organizations never replaced it with anything adequate.
The model that has replaced it is called identity-first security. And it starts from a fundamentally different assumption: every access request, even from your CFO working from their kitchen table, should be treated as potentially unverified until it is actively confirmed.
This is not about distrust in your people. This is about operational mathematics.
When a single employee's credentials are stolen through an AI-generated phishing email convincing enough to fool even an experienced professional, the critical question becomes how far an attacker can travel inside your cloud environment before someone notices.
Without granular access controls in place, the answer is typically: far enough to cause serious damage.
Every person on your team should have access to exactly what they need to perform their role, and nothing more. Not the access they had three years ago, which nobody ever reviewed. Not the permissions that were set up in a hurry during onboarding. The minimum viable access is actively enforced, with every session logged and auditable.
This is the foundation of a cloud environment built to scale without becoming a liability.
Your Own Team Is the Biggest Threat to Your Cloud Security
Here is the number that should change how you think about your cloud environment.
Ninety-five percent of cloud security failures in 2026 trace back to misconfiguration. Not to a flaw in your cloud provider's platform. Not to a sophisticated attack that no one could have anticipated. To a human error during a routine deployment that left a door open without anyone noticing.
Your cloud environment is not static. Developers push new configurations every sprint cycle. Teams spin up new instances on short notice. API keys get generated and then forgotten. Permissions get adjusted during a rushed release and are never reviewed again.
Each of those small changes is a potential crack in your security posture.
And the cruelest part is that these cracks are entirely invisible until they are not. The average time to detect a cloud breach in 2025 exceeded 200 days. Consider what 200 days of undetected access means for your customer data, your intellectual property, and your regulatory compliance standing.
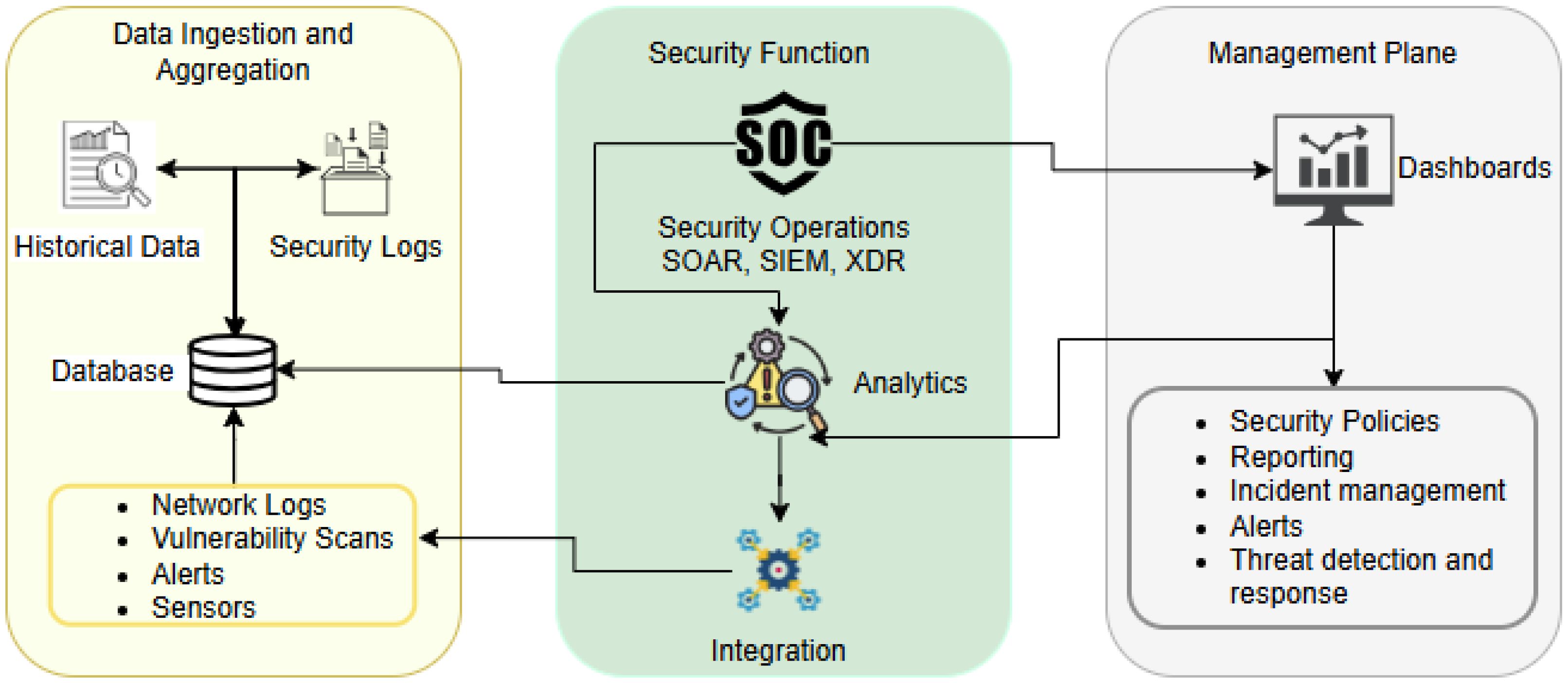
Automated Cloud Security Posture Management is no longer a sophisticated add-on for enterprise organizations. It is the operational baseline for any business running workloads in the cloud, regardless of size.
Think of it as a building inspector that never sleeps, never takes a day off, and never misses a detail. It scans your cloud environment continuously, flags every unauthorized change to your security settings, and escalates issues before a human would even notice the problem exists.
For organizations actively migrating to the cloud, this matters more than at any other phase. The migration window is precisely when misconfigurations happen most frequently and at the highest volume. Without automated detection running during migration, you are moving your organization's most sensitive data into an environment you cannot fully see.
DataManagement.AI's cloud migration platform embeds posture management directly into the migration workflow itself. Your security baseline is not something you configure after the migration is complete. It is established and enforced from day one, so the environment you build is the secure one you intended.
The 5 Cloud Security Failures You Are Probably Overlooking

1. You trust your cloud providers more than your architecture
Cloud providers secure infrastructure.
You are responsible for everything else.
This shared responsibility model is where most organizations fail.
You assume:
Storage is secure
Access is controlled
Configurations are optimized
But misconfigurations remain one of the biggest causes of breaches in cloud environments.
Your risk is not the platform.
It is how you use it.
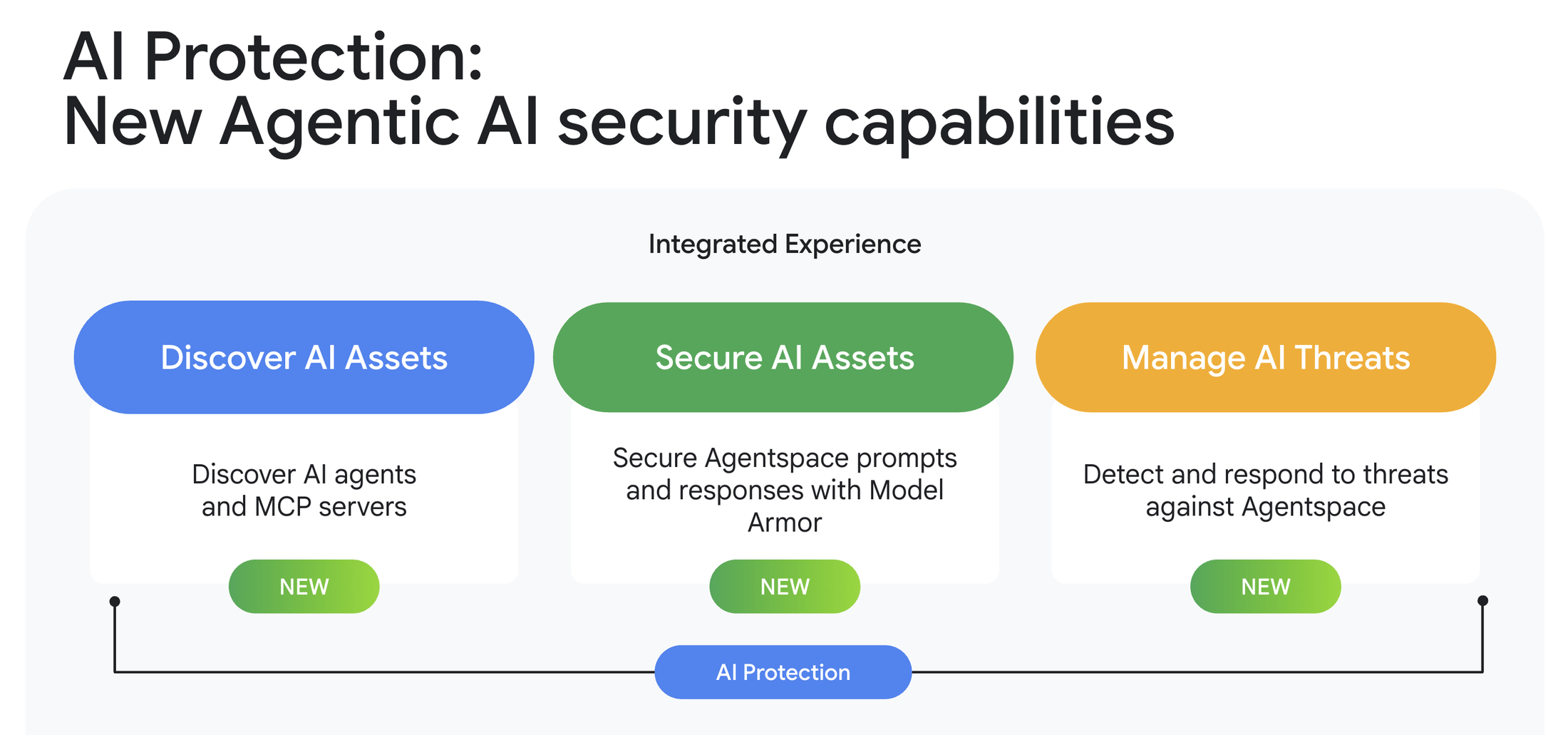
2. Your identity layer is your weakest link
In 2026, identity is the new perimeter.
If someone can access your system, they can move through it.
Weak identity controls lead to:
Unauthorized access
Lateral movement across systems
Data exposure without detection
This is why modern cloud security is shifting toward Zero Trust architectures, where nothing is trusted by default.
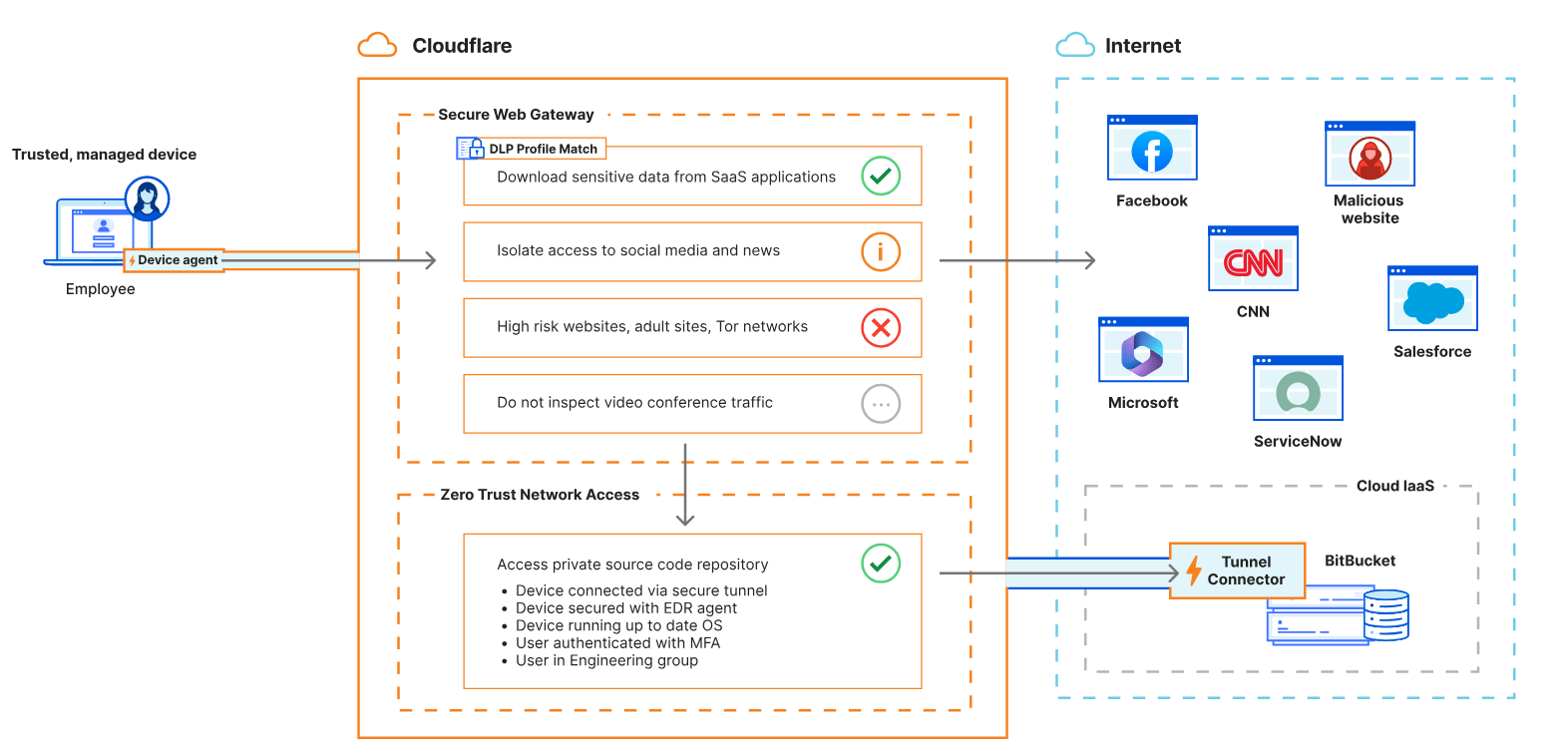
If you still rely on traditional access models, you are already behind.
3. Your cloud environment is more complex than your team can manage
Hybrid and multi-cloud are now standard.
Not because they are trendy.
Because they are necessary.

Most organizations now operate across:
Public cloud
Private infrastructure
Multiple vendors
This flexibility improves resilience.
But it also creates fragmentation.
Without structured governance, complexity becomes your biggest vulnerability.
4. You are reacting to threats instead of preventing them
Traditional security waits for alerts.
Modern cloud environments move too fast for that.
By the time a threat is detected manually, the damage is already done.
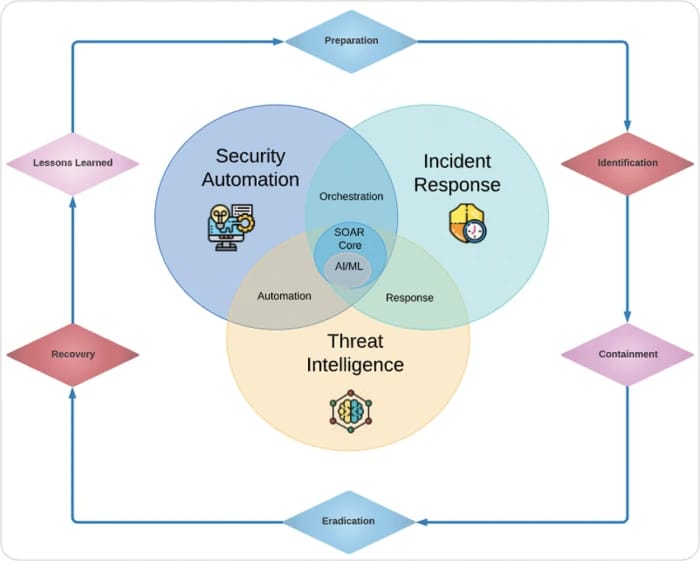
That is why leading organizations are shifting toward:
Continuous monitoring
Automated response systems
AI-driven threat detection
Because manual security no longer scales.
5. Your compliance strategy is slowing you down
Regulations are not optional anymore.
They are expanding across industries and regions.

You are now expected to prove:
Data protection controls
Access governance
Incident response readiness
Compliance is no longer a checkbox.
It is an ongoing operational requirement.
And if your cloud is not built for it, you will feel it in delays, audits, and penalties.
What Your Migration Strategy Is Still Missing
Most cloud migration projects are evaluated on three outcomes: cost reduction, performance improvement, and scalability. Security is treated as something that gets addressed once the migration is complete.
This sequencing is the root cause of most of the breach patterns described above.
Security cannot be effectively retrofitted onto a cloud environment that was not architected with it from the beginning. The identity permissions, the access controls, the behavioral monitoring, and the configuration management have to be built into the migration itself, not applied afterward.
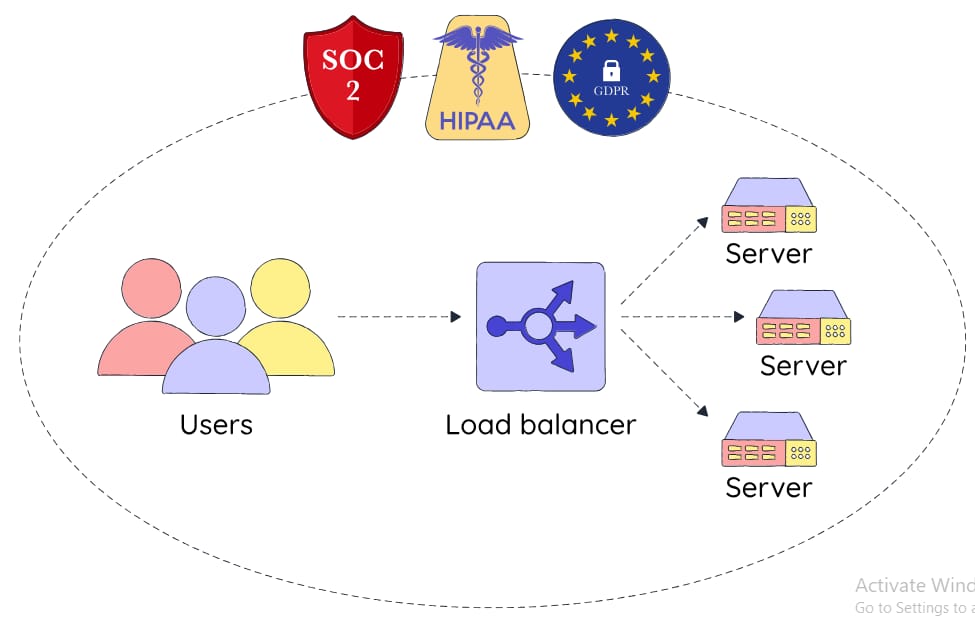
Compliance requirements are not getting simpler either. Whether your organization operates under HIPAA, SOC 2, GDPR, or sector-specific regulatory frameworks, the expectations in 2026 are more demanding and more actively enforced than in any previous year. Manual audits are too slow. Annual compliance reviews leave 364 days of unmonitored exposure in between.
Organizations maintaining genuine continuous compliance are the ones running platforms that make audit readiness a persistent default state, not a reactive scramble triggered by an upcoming review.
If your current migration plan does not include automated posture management, behavioral anomaly detection, enforced least-privilege access, and continuous compliance monitoring built into the workflow, your migration is creating a liability rather than resolving one.
The Organizations That Win in 2026 Are Building Differently Right Now
Cloud security is not an IT problem. It is a leadership decision with direct consequences for your organization's financial performance, customer trust, and long-term resilience.
Every week your organization operates in an improperly secured cloud environment is another week of compounding exposure. Regulatory risk. Operational fragility. Reputational vulnerability that can materialize faster than any PR strategy can respond to it.
The organizations pulling ahead of their competition right now are not doing so by moving faster. They are doing so by moving with confidence.
By building cloud infrastructure that their teams can actually use productively without creating unmanaged risk. By treating their data environment as the operational asset it is, rather than the administrative cost it used to be.
You have built something worth protecting. The infrastructure behind it should reflect that.
See exactly how DataManagement.AI builds security into your cloud migration from day one, so you scale without the liability. Book now and walk away with a clear picture of where your current environment stands.
Thank you for reading
DataMigration.AI & Team